Restricting the access is a critical feature required in any file system. The files are accessed either by a user, or an Azure Service or by a program. In this article, I will explain how to restrict the access of a user to a specific user in an ADLS.
The hierarchy of the file system inside ADLS is given below.
Storage account –> Container –> Folders / Files
The access control is possible through IAM roles till the level of containers. Beyond containers, we will need to control the access through ACLs. Any access given at the storage account will be present through out the storage account. Similarly, any access given at the container level will be applied to all the folders and files within the container.
Let us consider the below scenario.
storage account name – amalstore
container name – data
folders – folder1, folder2
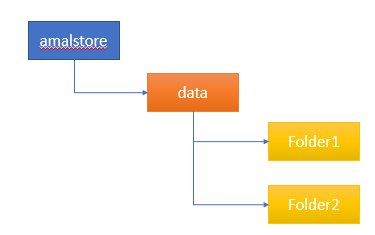
The requirement is to enable Read/Write access to the Folder1 alone to a specific user. We don’t want this user to access Folder2.
Solution
We will handle this access using ACLs.
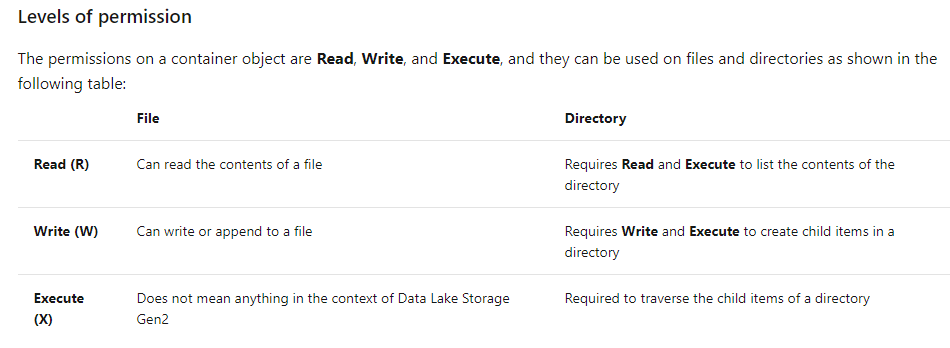
We need to give this user Execute privilege in the container and all the parent directories till Folder1 through ACL. After that enable RWX privilege in the Folder1 through ACL. In our case, we only have a container and a subfolder structure. If we have nested hierarchy, we will need to enable Execute privilege in all the parent folders. Execute privilege is required in all the parent directories for the traversal to the child directories / files. Read the snippet from the Azure documentation to get a clear understanding of the privileges in ACL.
The ACLs can be managed by clicking the three dots on the extreme right side of the container or folder in the storage browser.
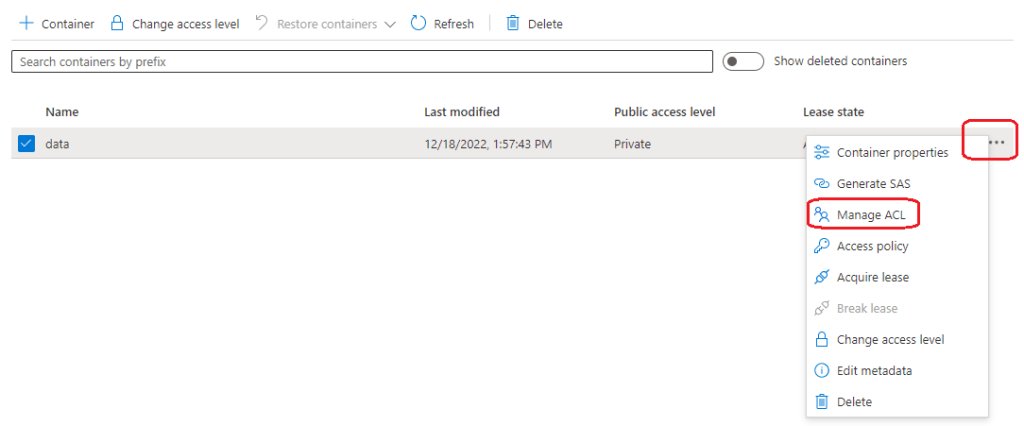
Click on the three dots and select the Manage ACL option. After that click on the Add Principle option. Here, in our case the principle is the user account which we need to enable the access. The principle can be a user account or a service principle. In our case, it is a user account. If you have limited access in the account, you will not be able to search user accounts or service principles in the list. You will have to specify the extract user id or service principle id.

Enable Execute(X) privilege in all the parent directories for the user and enable RWX privilege on the Folder1.

In this way, the user will be able to access only the folder1. The same can be configured for a service principle also. I hope this tip is helpful.
